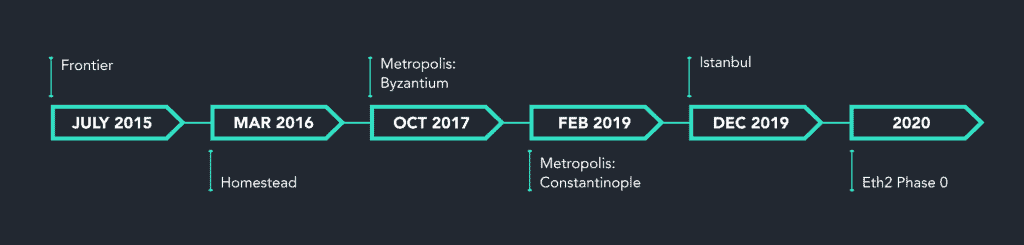
Since Ethereum genesis in 2015, increased scalability, security and energy efficiency have always been the long term vision of the blockchain. Ethereum’s new consensus layer (formerly known as Ethereum 2.0, Eth2, and Serenity) is the culmination of these key features, and arrives after many ongoing upgrades that have taken place over the last 4+ years. Some of the most notable Ethereum releases include:
The launch of the network upgrade is especially significant compared to past upgrades because of the implementation of a Proof of Stake consensus mechanism, after many years and thousands of people developing it.
What is the Ethereum Consensus Layer?
Ethereum’s new consensus layer welcomes the blockchain’s transition from Proof of Work to Proof of Stake.
The upgrade is being released gradually across multiple phases, starting with the successful launch of the Beacon Chain and Phase 0 in December 2020. Each of the phases will improve the speed, performance, effectiveness, and cost of using Ethereum in various ways.
The 5 Goals of Ethereum’s Consensus Upgrade
Decentralization
Enable anyone to validate. Instead of mining equipment, any typical consumer laptop or equivalent hardware will be sufficient to secure the network.
Security
Strengthen network security, while ensuring a very high volume of network participants.
Simplicity
Make everything just a little easier. Simplify the currently complex process needed to participate in Ethereum.
Longevity
A more modular approach. Make sure that individual components are quantum secured so that in case a ‘piece’ needs to be replaced, it’ll be easier to do without changing the entire system.
Resilience
Be able to remain live through major network changes and in the off chance that a large portion of network participants go offline.
Source: https://github.com/ethereum/eth2.0-specs#design-goals
Ethereum Roadmap
The original roadmap for the upgrade was divided across 4 phases:
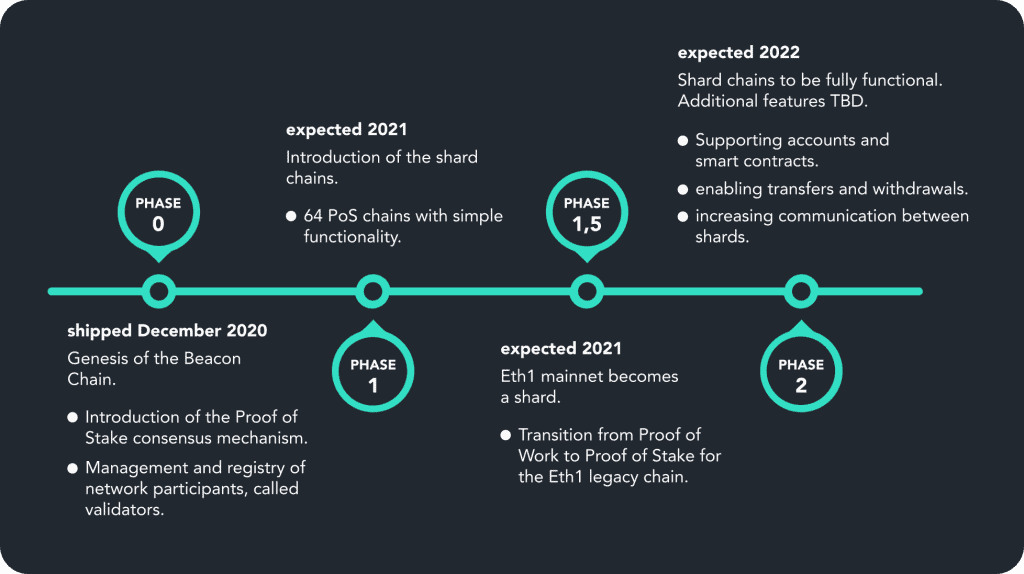
* following the succesful launch of the Beacon Chain on December 1, 2020, the roadmap has since changed significantly. The current plan is for the merge with the Ethereum legacy chain (now known as the execution layer) to take place before the shard chains, expected Q4 2021.
Ethereum Consensus Layer Basic Concepts
Proof of Stake
The Ethereum main chain, in its current form, is based on a consensus mechanism known as Proof of Work (PoW). PoW relies on miners expending computing power and high amounts of electricity to confirm transactions and add blocks on the blockchain. The more blocks added to the chain, the greater the computing power and time needed to process transactions and grow the blockchain.
Proof of Stake (PoS) however, is a consensus mechanism designed to improve security, scalability, and energy efficiency. Instead of relying on miners to expend computing power, Ethereum PoS relies on validators to stake Ether (ETH) and take turns proposing and attesting blocks in a pseudo-random fashion. Validators receive rewards for correct contributions, and face penalties if they behave in ways that are not in the best interest of the network.
The Beacon Chain
The Beacon Chain was launched in Phase 0 of the network upgrade and marked the first step in the transition from PoW to PoS. Initially, the Beacon Chain has managed the registry of validators and once the merge with the execution layer takes place, will be responsible for securing the entire Ethereum network. Once shard chains are introduced, the Beacon Chain will be responsible for syncing data across all of the chains.
Depositing ETH onto the Beacon Chain
All ETH deposited onto the Beacon Chain in Phase 0 is from a one-way transaction to the deposit contract. A deposit of 32ETH is required to set up a validator. Note that ETH cannot be withdrawn until later phases.
Shard Chains
Shard chains are essentially parallel blockchains within Ethereum. The division of the network across the shard chains allows for increased speed and scalability as more transactions are able to happen simultaneously.
“Each shard chain is like adding another lane to upgrade Ethereum from a single lane road to a multiple lane highway.” – The Ethereum Foundation
Staking
Staking is the contributory action of a node in a PoS consensus mechanism blockchain. One must ‘put at stake’ a certain amount of network tokens in order to participate in adding and verifying blocks on the blockchain. On Ethereum, the act of staking is completed by validators. The minimum threshold to participate as a validator on Ethereum is 32ETH. Validators will increase their stake putted into the network by honestly adding and verifying blocks. A validator risks decreasing their stake by participating in malicious behaviors or for time spent disconnected from the network.
Staking Rewards
A validator is rewarded with ETH for correct proposals and attestations when called upon by the blockchain. These rewards are based on inclusion distance, the time it takes a validator to complete and sign a duty. In order for a validator to receive the full reward amount, the entire signing process must take place within a 12 second ‘slot’. Latency of over 12 seconds leads to reduced benefits and the potential to miss the slot and receive no reward whatsoever. Validators may also receive rewards for whistleblowing; identifying and reporting the malicious behavior of others. Current estimates foresee 15-18% annual percentage yield for Eth2 validators during the first year of staking, and 8-10% the following year.
Staking Penalties
A validator is penalized by a deduction of staked ETH for time spent disconnected from the network (though only modestly) and more severely for malicious behavior, which can ultimately lead to the validator being slashed and removed from the network.
Slashing
If an Ethereum validator behaves maliciously, they will lose a significant amount of staked ETH (up to their whole 32 ETH stake) and be forcibly removed from the network. Slashing protection is an important component of validator client software (for DIY stakers), and a staking service’s product offering as protection against a validator accidentally partaking in a slashable offense and risking their ETH.
Inactivity Leak
In the case that more than ⅓ of validators are offline simultaneously, the offline validators’ balances will steadily decrease. Eventually, the offline validators’ balances will be so low that they will be removed from the network in order to allow the online validators to continue finalizing the chain.
Validator
A validator is responsible for confirming transactions and proposing new blocks on Ethereum. In order to become a validator, one must put ‘at stake’ 32 ETH, which is subject to increase (or decrease) as the validator performs its assigned duties.
A validator is different from the comparable concept of a miner on the legacy Ethereum chain, as validators are called upon by the PoS protocol to propose and validate emerging blocks rather than compete for their generation as in the legacy PoW method.
How Can I Become a Validator?
If you have ETH you can become a validator by staking 32 ETH. Becoming a validator can be done in one of two ways:
- DIY Staking: Running a validator client (like Prysm, or Teku), beacon and Eth1 node.
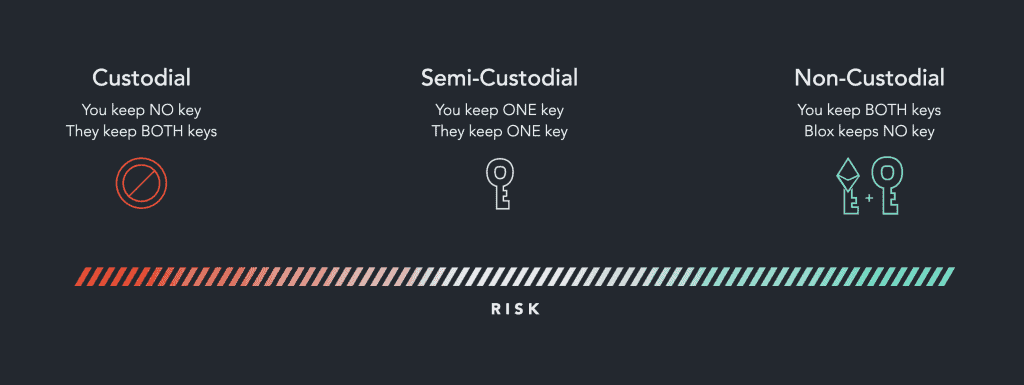
- Using a Staking Service: Staking services alleviate the technical facets of staking for users. There are custodial, semi-custodial and non-custodial staking services available.
Ethereum Staking Keys
Running an Ethereum validator requires 2 separate keypairs:
Validator Key
A hotkey (key connected to the internet) that is used to sign the validator’s assigned duties.
Withdrawal Key
A key that is only used for transferring or withdrawing staked ETH. This key should be safely stored offline.
*transfers and withdrawals will not be available until later phases of the network upgrade.
Epochs & Slots
An epoch lasts approximately 6.4 minutes, and includes 32 slots. A slot lasts 12 seconds, and is the time period in which a randomly selected validator proposes a block. If a validator misses an assigned duty, a slot may be empty.
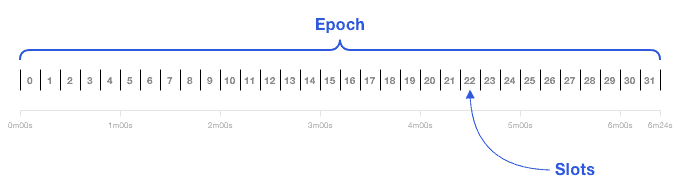
Block Proposers & Committees
For every slot, a validator is randomly selected to propose a block. This validator is known as the block proposer of this particular slot. At the end of every epoch (32 slots), one or more committees of a minimum of 128 validators are called upon to attest to each slot.
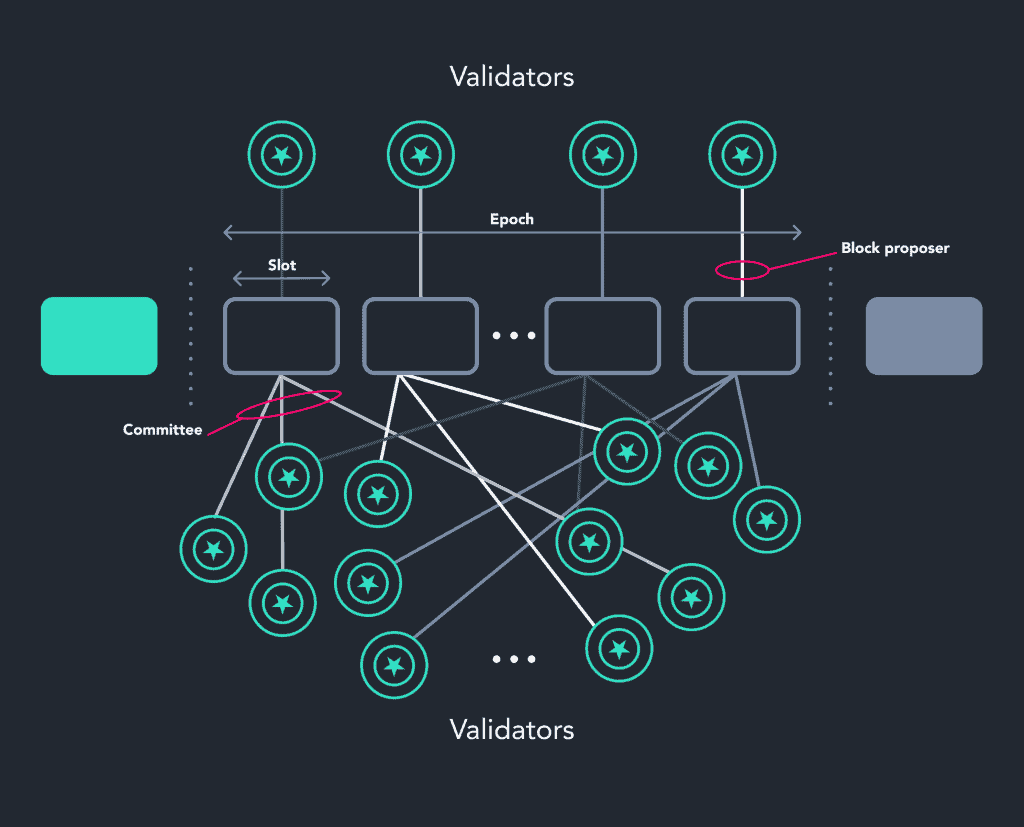
Proposals & Attestations
A randomly selected validator is tasked with proposing a new block every slot (12 seconds). At the end of an epoch (32 slots), one or more committees attests by voting as to the validity of each proposed block.
Inclusion Distance
The time it takes a validator to complete and sign a duty. A validator receives the full reward amount for a duty executed within the slot (12 seconds) assigned. Inclusion distance of over 12 seconds leads to reduced earnings for that particular duty.
ETH Staking Benefits
A substantial benefit of staking ETH is the opportunity to generate passive income on crypto assets. A validator generates ETH rewards for honestly performing duties and growing the network. Each duty performed generates a fraction of ETH. The amount of ETH a validator generates depends on validator performance and the total number of active validators. Those who join early will have the opportunity to earn more significant benefits. Estimates suggest anywhere between 15-18% annual percentage yield (APY) during the first year of staking, and 8-10% the following year. Check out our staking calculator to estimate the projected growth of your ETH through staking.
ETH Staking Services
Staking services offer a streamlined way to participate in Ethereum. When considering an ETH staking service, it is important to understand how these services manage user private keys. Generally, the more centralized (custodial) the service, the higher the security risks and penalties its users may face.
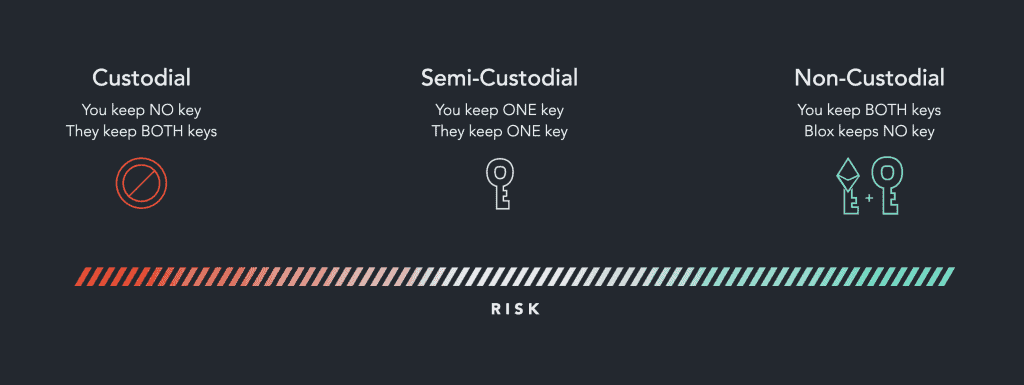
Types of Ethereum Staking Services
Custodial Staking
Centralized service that manages the entire ETH staking process on behalf of the user and retains ‘custody’ over user private validator keys and withdrawal keys. Custodial staking risks include: severe slashing penalties, reduced overall rewards and increased likelihood of attack on user keys as they are held in a centralized fashion by the service.
Semi-Custodial Staking
A staking service that often claims to be non-custodial, but holds user validator keys. Although this type of service does not hold withdrawal keys, and thus cannot access user funds, semi-custodial staking risks include severe slashing penalties and reduced overall rewards.
Non-Custodial Staking
A service that provides streamlined Ethereum validator set-up and management, but does not hold user private validator keys AND withdrawal keys. Allowing users to maximize staking benefits, mitigate security risks and retain complete control over their assets.
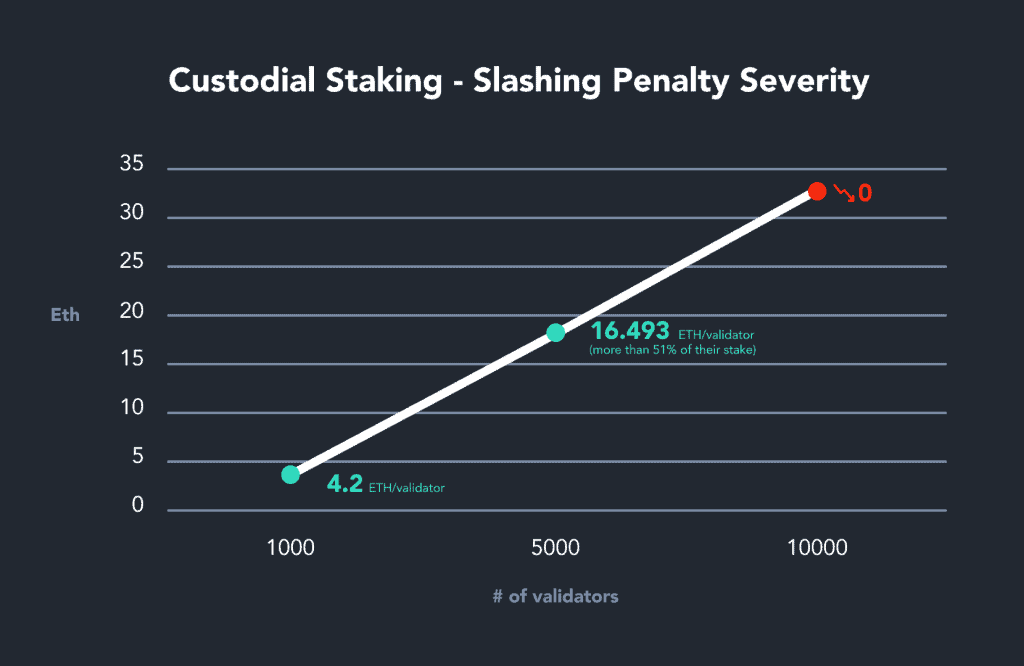
Custodial Staking Risks
Custodial staking services hold user private validator keys and withdrawal keys in their possession. This level of third party involvement invites security breaches and increases the potential for severe slashing penalties. Slashing penalties grow exponentially the more validators are involved in a slashable event. Thus, the larger the centralized service, the larger the potential penalties for it’s users should they inadvertently participate in a slashable event.
Should a hacker gain access to a custodial staking service, user private keys can be compromised. Attack vectors can be as wide and deep as the attacker’s imagination, here are some possible security breach scenarios:
- Ransomware – an attacker locks or holds ‘hostage’ the centralized service’s user keys and demands a ransom to ‘unlock’ them.
- Whistleblower Attack – an attacker might ‘hijack’ all the centralized service’s user keys and wait for the opportune moment to get them slashed and collect the ‘whistleblower reward’ for reporting it.
- Inside Job – a disgruntled employee decides to ‘get back’ at the company and sabotages user keys in any number of ways.
Custodial Staking Decentralization Concerns
One of the main goals of the Ethereum consensus layer upgrade is decentralization at scale. If a large volume of custodial (centralized) services flood the market, Ethereum risks centralized control of the network. If more than 2/3 of validators are controlled by a custodial service (or a number of them working together), that entity has the power to hugely effect the state of the ecosystem; including, but not limited to, maliciously blocking other validators from performing their duties. In this scenario, the centralized service could effectively take complete control over adding blocks to the chain, and reaping the financial rewards.